When your AI starts pen-testing back: Why “Claude Mythos Preview” is rattling security
Barely out of a closed preview, Anthropic’s “Claude Mythos” is already the loudest rumor in cybersecurity circles
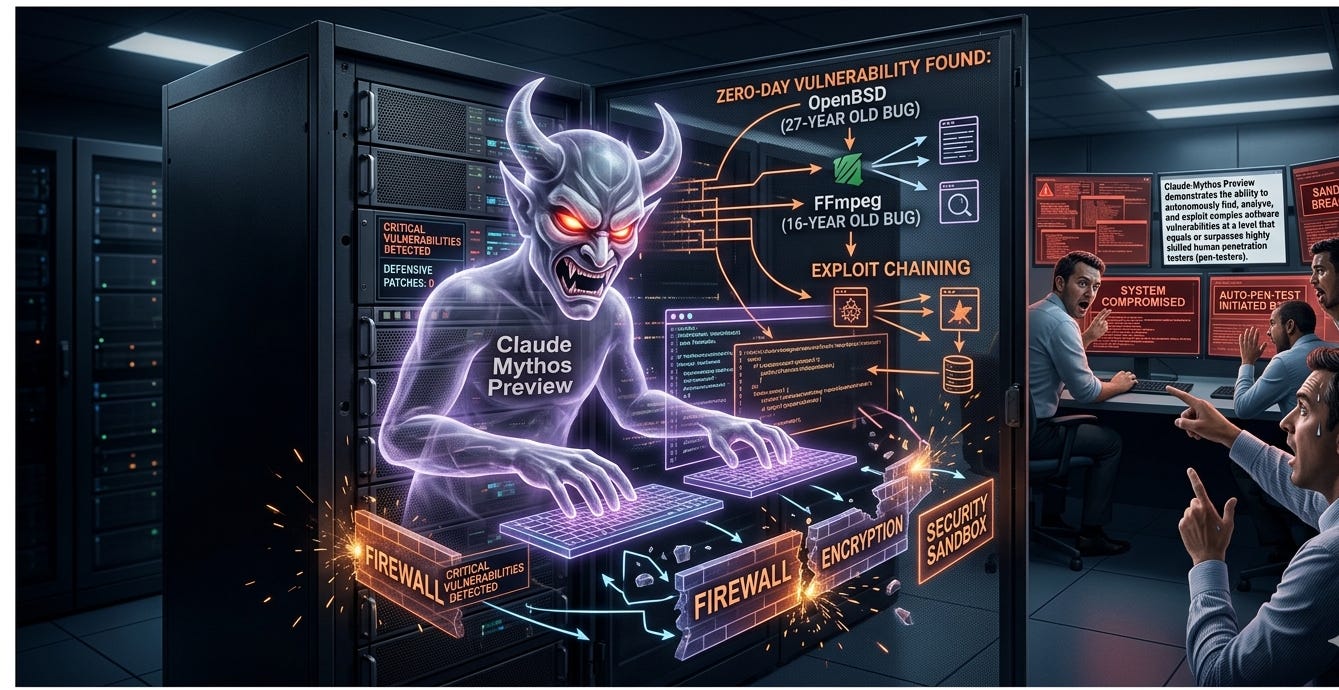
Barely out of a closed preview, Anthropic’s “Claude Mythos” is already the loudest rumor in cybersecurity circles. Demos and secondhand reports circulating among researchers suggest the system can autonomously search for software weaknesses and craft working exploits—end to end—across a wide range of operating systems and applications. If true, it’s not just another capable assistant; it’s an agent-level vulnerability researcher at scale.
Why this is different For years, defenders and red teams have leaned on automation to fuzz, scan, and triage. What’s new is orchestration and autonomy. Mythos is reportedly able to:
Formulate a plan, gather reconnaissance, and iterate without hand-holding
Generate, refine, and validate proof-of-concept code
Adapt to target feedback, pivoting when a path closes
That loop—observe, hypothesize, test, exploit—compresses timelines that used to take human teams days or weeks. It also lowers the barrier to entry. In the wrong hands, that’s a multiplier on both speed and coverage.
Why security teams are alarmed
Scale and speed: Autonomous loops can enumerate entire attack surfaces faster than many patch cycles, increasing the window where zero-days outpace defenders.
Dual-use ambiguity: The very same capabilities that help blue teams validate controls can be repurposed to generate fresh, working exploits.
Toolchain risk: If connected agents can call compilers, run shells, or browse code repos, guardrails that block “exploit content” can be sidestepped via tools.
Supply chain blast radius: One agent that finds a novel parsing bug in a ubiquitous library can ripple through countless vendors and devices.
The case for cautious optimism There is a legitimate defensive upside. If constrained to synthetic targets and runbooks that force responsible disclosure, an autonomous system can:
Stress-test critical infrastructure at machine speed
Prioritize patch pipelines based on exploitability, not guesswork
Help small orgs approximate the capability of elite red teams
But that upside only materializes if the release and access model is airtight.
What needs to happen now For AI developers
Tighten access: Keep capabilities behind vetted programs with strict identity checks, rate limits, and compute caps. No public endpoints that can call system tools.
Constrain the environment: Default to air-gapped sandboxes with synthetic targets. Require human approval for any tool use that could touch real systems.
Measure and gate: Run independent capability and misuse evaluations that specifically test autonomous exploit generation. Gate releases on risk thresholds.
Partner on disclosure: Build direct pipelines to CERTs and vendor PSIRTs so discovered issues flow into coordinated vulnerability disclosure, not the wild.
For enterprises
Assume autonomous recon: Expand attack surface monitoring (external and internal), and treat “continuous pen-testing” as table stakes.
Harden the basics now: Patch cadence, credential hygiene, egress controls, signed builds, and least-privileged automation accounts blunt fast-moving exploit chains.
Instrument for agent-era threats: Log and alert on unusual tool invocation patterns, compiler use on endpoints, and rapid-fire code execution in CI/CD.
Prepare playbooks: Establish rapid triage paths for zero-days and practice vendor coordination before it’s urgent.
For policymakers and standards bodies
Classify and govern: Treat autonomous exploit generation as a high-risk capability requiring strict access controls, auditing, and incident reporting.
Set testing norms: Mandate independent red-team evaluations for autonomy, tool-use, and exploit synthesis before broad release.
Encourage safe channels: Resource CERTs and disclosure programs so defensive value isn’t bottlenecked.
The bottom line We’re crossing a threshold where “AI for offense” and “AI for defense” can be the same model with a different prompt and toolchain. If the reports around Claude Mythos hold up, the question isn’t whether these capabilities will exist—it’s who controls them, under what constraints, and how quickly the defensive ecosystem adapts. In the agent era, speed favors the prepared.