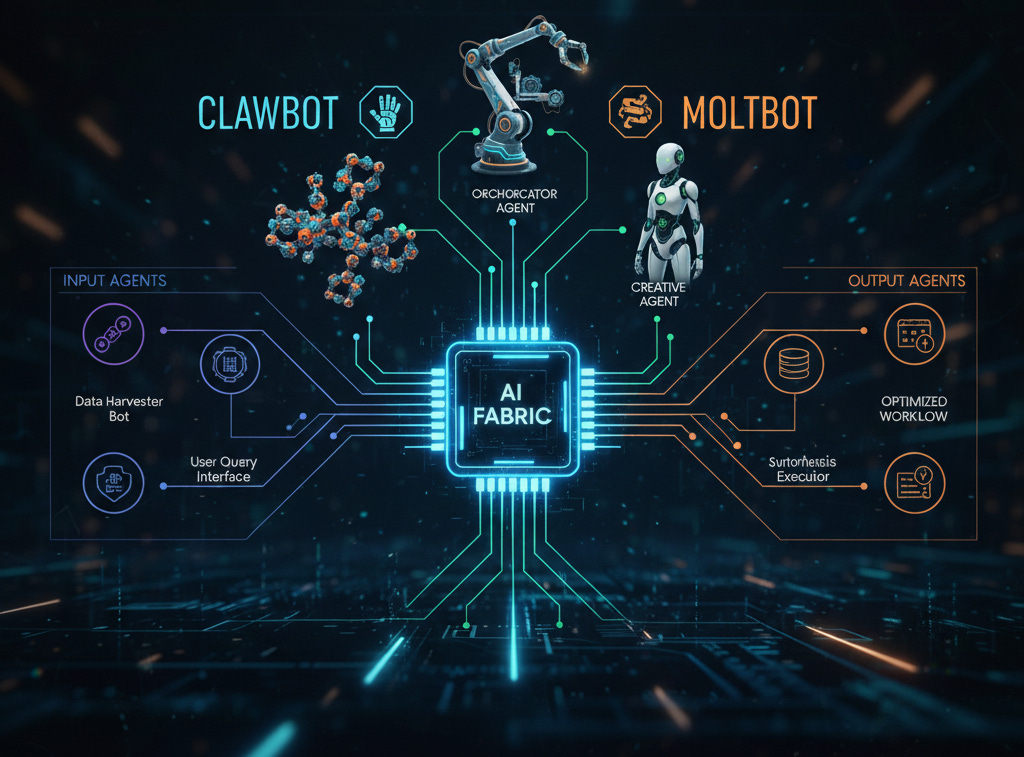
Clawbot: the AI “moltbot” everyone’s talking about
Bottom line Clawbot earns the “moltbot” nickname by shedding toil and emerging with safer, cleaner systems. Used with sane guardrails, it turns scattered signals into shippable fixes—true or false.
Clawbot: the AI “moltbot” everyone’s talking about
If 2025 has a breakout AI agent, it’s Clawbot—the so‑called “moltbot” that sheds busywork, digs into your stack, and rebuilds what’s broken. Think of it as a hands-on teammate that reads your code, roams your cloud, and turns messy alerts into clean fixes—with receipts.
What Clawbot can do
Codebase concierge: Maps large repos, flags smells, writes tests, drafts refactors, and opens ready-to-review PRs.
Security sidekick: Scans dependencies, IaC, containers, and cloud posture; correlates issues into attack paths; proposes least‑privilege policies.
Ops autopilot: Turns runbooks into actions—rotates keys, patches images, closes ports, and rolls forward with health checks.
API and UI tester: Generates fuzz and contract tests, catches breaking changes, and suggests safer defaults.
Knowledge runner: Ingests docs, tickets, and logs and answers with cited sources, not guesses.
Workflow glue: Works in Slack/Jira/GitHub, tags owners, drafts incident timelines, and tracks remediation to done.
Security findings it’s surfacing Early adopters report Clawbot excels at connecting dots you already have:
Secrets exposure: Hardcoded credentials in CI logs, .env files, and mobile build artifacts; auto‑rotates and PRs a fix.
Cloud misconfig: Public S3/GCS buckets, wildcard IAM roles, and permissive security groups; replaces with scoped roles and condition keys.
Supply chain risk: Typosquatted packages and vulnerable transitive deps; upgrades with SBOM notes and compatibility diffs.
OAuth/OIDC pitfalls: Missing PKCE, over‑broad redirect URIs, and token lifetimes that invite replay; ships secure config templates.
SSRF and metadata: Unvetted URL fetchers reaching instance metadata; adds egress allowlists and safe HTTP clients.
CORS and auth gaps: Wildcard origins and preflight leaks; proposes route‑level checks and tightened headers.
Shadow admin: Group nesting that grants surprise privileges; recommends split‑roles and guardrails.
Insecure defaults: Exposable dashboards (Grafana, Prometheus), forgotten staging subdomains, debug endpoints left on.
CI/CD drift: Long‑lived deploy keys, unpinned actions, and artifact poisoning paths; pins, scopes, and rotates.
How it reports (and fixes)
Evidence first: Shows the file, policy, or endpoint in question with a minimal proof of exposure—no risky exploit steps.
Risk and blast radius: Explains “what an attacker could do next,” tying issues into attack paths across code, cloud, and CI.
Remediation you can ship: Generates patches, Terraform diffs, policy updates, and migration steps; opens PRs with tests.
Human-in-the-loop: Requires approvals, supports staged rollouts, and rolls back on health regressions.
Why teams like it
Context over noise: Correlates alerts so you fix causes, not symptoms.
Speed without the cliff: Sandboxed tool use, read‑only by default, and least‑privilege tokens keep it safe to try.
Explainable: Every action comes with a plan and plain‑English rationale.
Real-world snapshots
A fintech trimmed P1 misconfigs by 68% in a week by letting Clawbot rewrite overbroad IAM and seal public buckets—via PRs only.
A marketplace stamped out secret sprawl across CI and mobile builds, rotating keys and adding pre‑commit hooks.
A SaaS vendor killed a latent SSRF path and tightened CORS while bumping a vulnerable base image—zero downtime.
Practical cautions
It’s powerful, not omniscient: Treat findings like a sharp junior analyst—review diffs, verify impact.
Scope access: Start read‑only on code, cloud, and CI; enable writes per-repo with branch protections.
Watch for false positives: Tune rules, tag owners, and iterate on ignore lists like you would any scanner.
How to try it responsibly
Begin in audit mode on one service: repo + IaC + cloud posture.
Triage top five issues with owners; merge one or two low‑risk PRs.
Add runbooks for recurring tasks (key rotation, image bumps) and measure MTTR.
Expand scope gradually; keep approvals mandatory.
Bottom line Clawbot earns the “moltbot” nickname by shedding toil and emerging with safer, cleaner systems. Used with sane guardrails, it turns scattered signals into shippable fixes—and that’s why everyone’s talking about it.