AI agents - why security
When AI Agents Become Coworkers, Your Attack Surface Gets a Promotion
Your new AI agent books travel, files tickets, queries finance, and drafts emails. It also browses the web, reads internal wikis, and talks to other bots. It’s helpful—until it isn’t. Unlike traditional apps, agents make decisions, chain tools together, and learn from what they see. That autonomy is exactly what creates a fresh class of enterprise security risks.
What’s new and risky about agents
Over-permissioned tool use: Connectors to CRM, ERP, code repos, and file shares often start with broad scopes. An agent that can “read everything” can exfiltrate everything.
Prompt injection and tool hijack: A web page, customer email, or wiki page can quietly instruct an agent to send out secrets or reconfigure systems. RAG makes this worse if your corpus is untrusted or poisoned.
Memory that never forgets: Agents store conversation history and embeddings. Secrets, PII, and credentials can end up in long-lived vector stores and show up in later contexts.
Hallucinations with real consequences: “Confidently wrong” actions can submit invoices, merge code, or disable alerts when tool use is automated.
Identity ambiguity: Whose identity is the agent using? If tokens are shared or delegated opaquely, you lose auditability and blast radius control.
Agent-to-agent escalation: ChatOps bots, ticketing automations, and integration triggers can form loops that amplify a bad instruction into a company-wide event.
Supply chain exposure: Third-party plugins, tools, and models can be malicious or compromised. An innocuous “calendar” plugin might also request email and drive scopes.
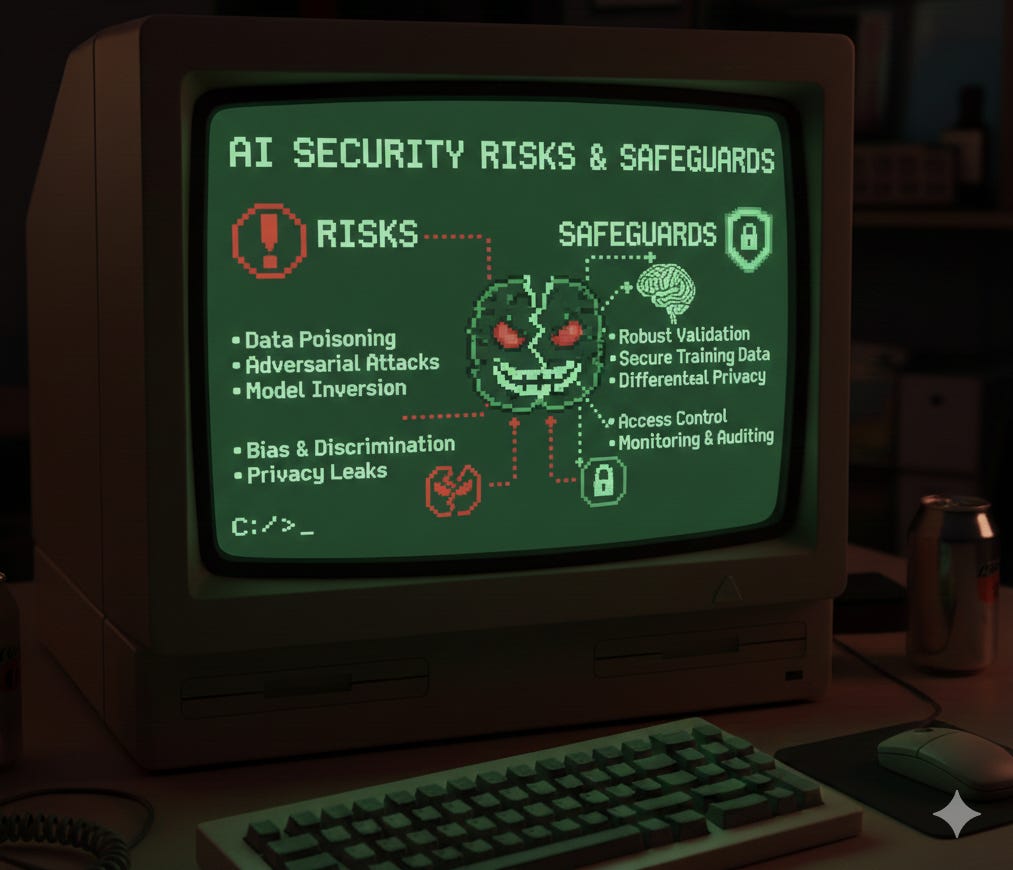
Data and model poisoning: Fine-tuning, feedback loops, or embedding corpora can be seeded to bias outcomes or plant backdoors.
Practical defenses that match how agents work
Treat agents like service accounts: Create a distinct identity per agent with least-privilege OAuth scopes, resource-level permissions, and short-lived tokens by default.
Isolate aggressively: Run agents in sandboxed execution with egress controls, DNS and network allowlists, and separate secrets per environment. Default tools to read-only.
Put humans in the loop for impact: Require approvals for high-risk actions (payments, code merges, policy changes). Use multi-party controls where feasible.
Policy-as-code for tool calls: Enforce who/what/when rules on each tool invocation. Validate inputs/outputs, constrain arguments, and block sensitive actions after untrusted inputs.
Semantic firewalls and content trust: Strip or neutralize instructions found in content. Prefer verified sources, signed documents, and curated RAG corpora over open web crawling.
Memory hygiene: Redact secrets before storage, encrypt vector DBs, set TTLs, and segment embeddings by tenant and sensitivity. Offer “off the record” modes.
Observability and audit: Log full decision traces—prompts, tool calls, responses, and model versions. Monitor for anomalies like unusual data access or tool chaining.
Red team for agents: Simulate prompt injection, jailbreaks, tool hijacks, and agent-to-agent cascades. Add canary secrets and measurable evals into CI for prompt and policy changes.
Secure the agent supply chain: Vet plugins, pin versions, demand SBOMs for tools and models, and verify model provenance. Review marketplace permissions like you would mobile apps.
Kill switch and key rotation: Be able to pause an agent instantly, revoke its tokens, roll secrets, and purge or quarantine its memory. Practice the playbook.
Shadow AI controls: Inventory agents with a central registry, require reviews before production access, and block unknown agents at the network and SaaS layers.
Train the humans: Teach teams not to paste secrets, recognize injection patterns, and escalate odd agent behavior quickly.
The takeaway Agents aren’t just another interface to the same systems—they’re new actors with initiative. Give them identity, boundaries, supervision, and audit the way you would a contractor with root access and a corporate card. Move fast, but instrument faster.